Best Interior Design Free Software Modular Design Of Secure Yet Practical Cryptographic Protocols
Find, Read, And Discover Best Interior Design Free Software Modular Design Of Secure Yet Practical Cryptographic Protocols, Such Us:
- The Definitive Guide To Encryption Key Management Fundamentals Best Interior Design Free Software Modular Design Of Secure Yet Practical Cryptographic Protocols,
- Https Www Securityindustry Org Wp Content Uploads 2018 08 Bacs Report Final Intelligent Building Management Systems Pdf Best Interior Design Free Software Modular Design Of Secure Yet Practical Cryptographic Protocols,
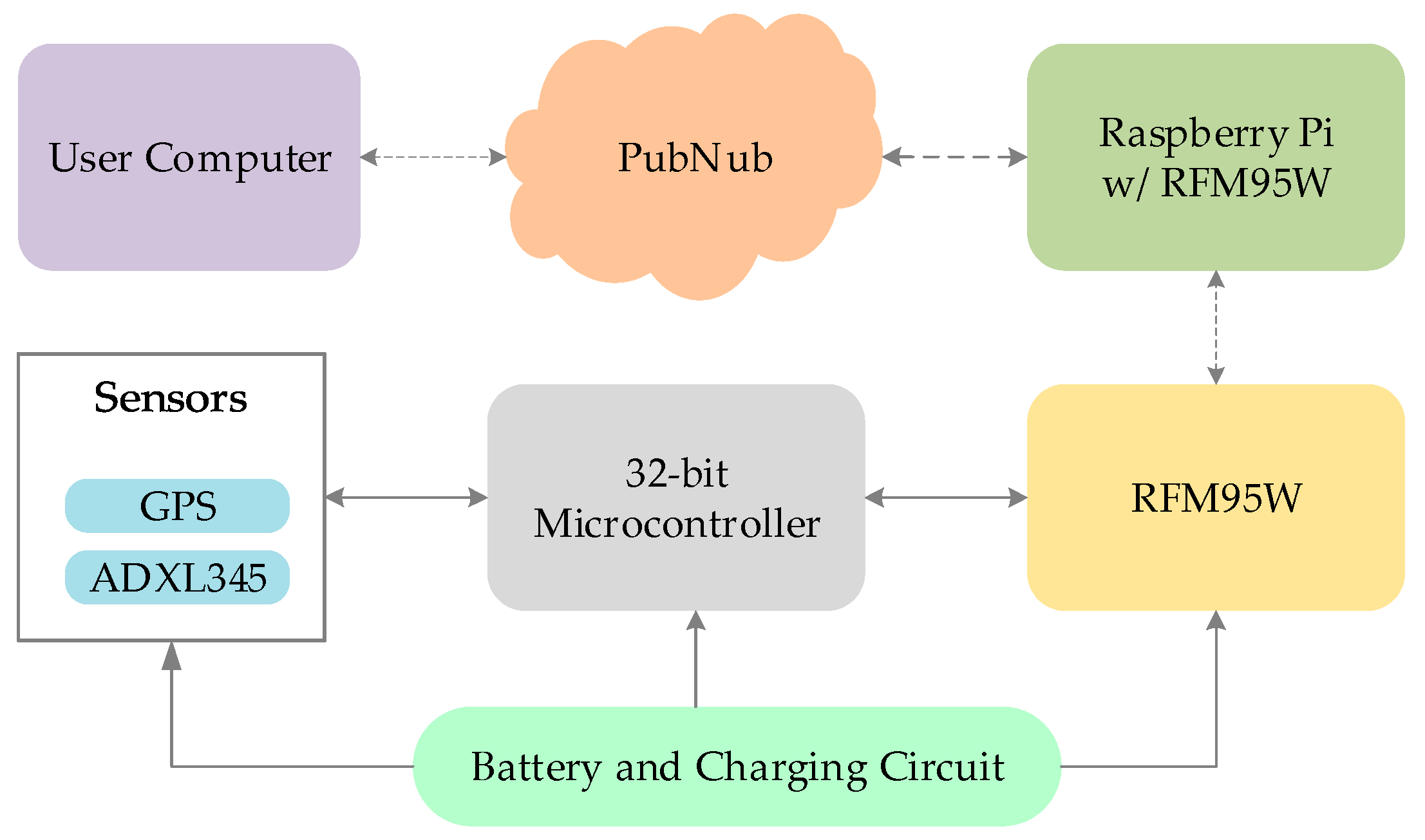
- Sensors Free Full Text Rapidly Deployable Iot Architecture With Data Security Implementation And Experimental Evaluation Html Best Interior Design Free Software Modular Design Of Secure Yet Practical Cryptographic Protocols,
- Secure Multiparty Computation And Trusted Hardware Examining Adoption Challenges And Opportunities Best Interior Design Free Software Modular Design Of Secure Yet Practical Cryptographic Protocols,
- Sensors Free Full Text Rapidly Deployable Iot Architecture With Data Security Implementation And Experimental Evaluation Html Best Interior Design Free Software Modular Design Of Secure Yet Practical Cryptographic Protocols,
Best Interior Design Free Software Modular Design Of Secure Yet Practical Cryptographic Protocols, Indeed recently has been hunted by consumers around us, perhaps one of you personally. People now are accustomed to using the internet in gadgets to view video and image information for inspiration, and according to the name of this article I will discuss about
- House Interior Design Grey Modular Kitchen How To Make
- Interior Design Ideas Living Room Modern Modular Design Exists Only In Tangible Products It Makes No Sense In Services True False
- Interior Design House Design Modular Sofa Definition
- Interior Room Design Vector Modular Learning Kinder
- House Interior Design Photos Kitchen Modular Photo
If the posting of this site is beneficial to our suport by spreading article posts of this site to social media marketing accounts which you have such as for example Facebook, Instagram and others or can also bookmark this blog page.

The Definitive Guide To Encryption Key Management Fundamentals House Interior Design Photos Kitchen Modular Photo
Practical Cryptography P W Ws Amazon Co Uk Ferguson Niels Schneier Bruce 9780471223573 Books House Interior Design Photos Kitchen Modular Photo
National security agency and the us.
House interior design photos kitchen modular photo. Scientific and government protocols to techniques for investigation and. Before entering the field of computer security he worked as a navy helicopter search and rescue crewman whitewater raft guide chef martial arts instructor cartographer and network designer. Furniture design for singles.
48 out of 5. A practical guide to digital forensics investigations second edition presents more hands on activities and case studies than any book of its kind including short questions essay questions and discussion questions in every chapterit addresses issues ranging from device hardware and software to law privacy and ethics. Translate logical data model for target dbms d 5.
The book covers the important new algorithms ccm and gcm which simultaneously provide confidentiality and data integrity. D summary of the database design methodology for relational databases d 1. Build logical data model d 2.
Inside network perimeter security 2nd edition. Choose from the best furniture designs that are functional classy and perfect for compact spaces. Emphasizing both the fundamental principles as well as the critical role of performance in driving protocol and network design it explores in detail.
Before this course i have covered many other python courses but this course provides in depth explanations for python basics which made me better understand how python actually works. Sleek forms with folding surfaces and clever details are a striking yet practical choice. Design security mechanisms d 5.
Design user views d 5. Design file organizations and indexes d 5. Urban ladders small room furniture designs are multifunctional create a clutter free ambience and offer greater value.
While the exact nature of viruses had yet to be determined there was a new appreciation and fear of the havoc caused by bacteria which in turn drove a new clean revolution in interior design and sanitation created to rid interior spaces of dangerous disease spreading germs. Applications and standards introduces students to the critical importance of internet security in our age of universal electronic connectivityamidst viruses hackers and electronic fraud organizations and individuals are constantly at risk of. Build conceptual data model d 1.
With a focus on the most current technology and a convenient modular format this best selling text offers a clear and comprehensive survey of the entire data and computer communications field. 4 months 11 hours per week. Stephen northcutt is a graduate of mary washington college.
Innovations and improvements. Department of homeland security. You can sign up here.
For courses in corporate computer and network security. Although the sha 3 algorithm has yet to be selected it is important for the student to have a grasp of the design criteria for this forthcoming cryptographic hash standard.
More From House Interior Design Photos Kitchen Modular Photo
- House Design With Blueprint Modular Home Utah
- House Interior Design For 2bhk Modular Kitchen Gas Cylinder Storage
- Interior Design Name Ideas
- Online Interior Design Bachelor Degree
- Online Interior Design Business
Incoming Search Terms:
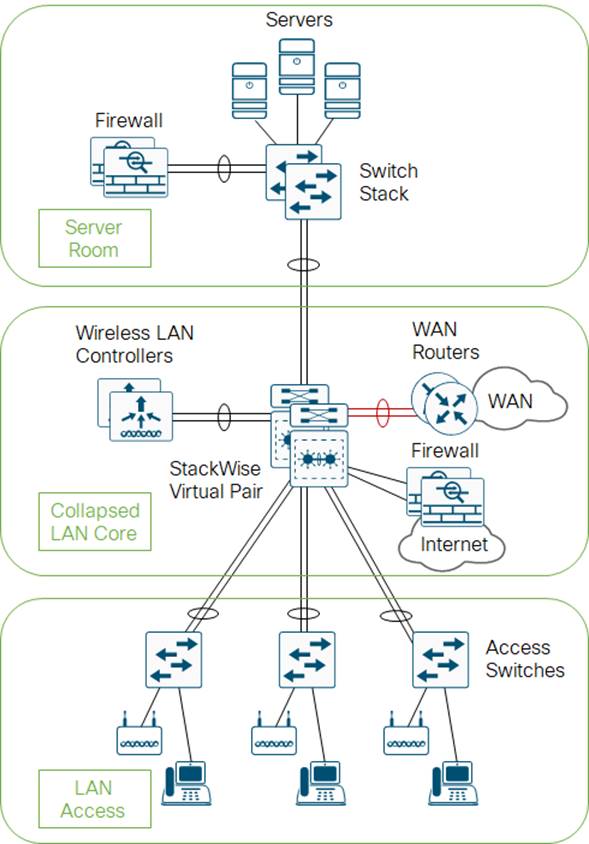
- Design Zone For Campus Campus Lan And Wireless Lan Solution Design Guide Cisco Online Interior Design Business,
- A Deep Dive On End To End Encryption How Do Public Key Encryption Systems Work Surveillance Self Defense Online Interior Design Business,
- Https Services Google Com Fh Files Misc Security Whitepapers March2018 Pdf Online Interior Design Business,
- Practical Cryptography P W Ws Amazon Co Uk Ferguson Niels Schneier Bruce 9780471223573 Books Online Interior Design Business,
- Cryptography Wikipedia Online Interior Design Business,
- Http Citeseerx Ist Psu Edu Viewdoc Download Jsessionid F155a72d1cb1878036d9e3a962956f49 Doi 10 1 1 81 5931 Rep Rep1 Type Pdf Online Interior Design Business,